Fake News Detection Using LSTM in TensorFlow and Deep Learning

DOI:
https://doi.org/10.54060/jase.v3i2.35Keywords:
Machine Learning, Artificial Intelligence, Deep Learning, Fake News, Python, Long Short-Term Memory, Convolution Neural Network, Preprocessing, Tokenization, Word Embedding, PaddingAbstract
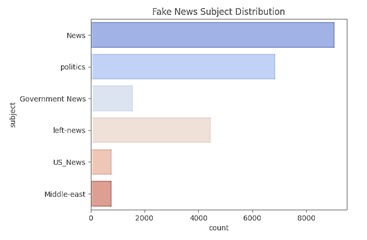
Today's culture has seen a significant rise in fake news, especially with the emergence of social media platforms where misinformation may spread swiftly. False information may have detrimental effects, such as influencing elections, encouraging hate speech, and eroding trust in reliable news sources. Identification of false news has become a hot topic in recent years, with several solutions being proposed for the problem. The paper discusses LSTM (Long Short-Term Memory), Bidirectional LSTM (BiLSTM), and Convolu-tion Neural Network (CNN)-based deep learning-based algorithms for identifying fake news. The "ISOT Fake News dataset," "News Dataset from TI-CNN," and "Getting Real About Fake News dataset" are among the datasets that were used. Following prepro-cessing methods such as stop keyword removal, stemming, and tokenization are used, these datasets are subjected to word embedding. This processed data is used to train the LSTM model, which determines whether or not news reports are fake. Performance metrics including precision, recall, accuracy, and F1-score provide as proof of the rec-ommended model's efficacy in identifying fake news. Comparisons with other state-of-the-art models show its improved efficacy. In terms of both accuracy and F1-score, the CNN beat the standard LSTM and BiLSTM models. CNN-BiLSTM is most effective model, having superior findings as well as efficiency across the three datasets.
Downloads
References
R. K. Kaliyar, “Fake News Detection Using A Deep Neural Network,” IEEE Xplore, 2018. https://ieeexplore.ieee.org/abstract/document/8777343/
Shu, K., Sliva, A., Wang, S., Tang, J., & Liu, H. (2017). “Fake news detection on social media: A data mining perspective.” ACM SIGKDD explorations newsletter, vol. 19 no. 1, pp. 22-36, 2017.
J. C. S. Reis, A. Correia, F. Murai, A. Veloso, and F. Benevenuto, “Supervised learning for fake news detection,” IEEE Intell. Syst., vol. 34, no. 2, pp. 76–81, 2019.
H. Jwa, D. Oh, K. Park, J. M. Kang, & H. Lim, “exBAKE: automatic fake news detection model based on bidirectional encoder representations from transformers (BERT),” Applied Sciences, vol. 9 no. 19, pp. 4062, 2019.
T. Hofmann, B. Schölkopf, and A. J. Smola, “Kernel methods in machine learning,” Ann. Stat., vol. 36, no. 3, pp. 1171–1220, 2008.
S. Akhtar, F. Hussain, F.R. Raja et al., “Improving mispronunciation detection of Arabic words for non-native learners using deep convolutional neural network features,” Electronics (Basel), vol. 9, no. 6, p. 963, 2020.
S. Hakak, M. Alazab, S. Khan, T. R. Gadekallu, P. K. R. Maddikunta, and W. Z. Khan, “An ensemble machine learning approach through effective feature extraction to classify fake news,” Future Gener. Comput. Syst., vol. 117, pp. 47–58, 2021.
S. Kula, M. Choraś, R. Kozik, P. Ksieniewicz, and M. Woźniak, “Sentiment analysis for fake news detection by means of neural networks,” in Lecture Notes in Computer Science, Cham: Springer International Publishing, 2020, pp. 653–666.
H. Ahmed, I. Traore, and S. Saad, “Detecting opinion spams and fake news using text classification,” Secur. Priv., vol. 1, no. 1, p. e9, 2018.
V. Kecman, Support Vector Machines-An Introduction in “Support Vector Machines: Theory and Applications.” New York City, NY, USA: Springer, 2005.
M. Viviani and G. Pasi, “Credibility in social media: opinions, news, and health information-a survey,” Wiley Interdisciplinary Reviews: Data Mining and Knowledge Discovery, vol. 7, no. 5, p. e1209, 2017, doi: https://doi.org/10.1002/widm.1209.
E. Wishart, “A wire agency journalist’s perspective on ‘fake news,” Media Asia, vol. 44, no. 2, pp. 102–106, 2017, doi: https://doi.org/10.1080/01296612.2017.1455624.
V. Gjylbegaj, “FAKE NEWS IN THE AGE OF SOCIAL MEDIA,” IJASOS- International E-journal of Advances in Social Sciences, vol. 4, no. 11, pp. 383–391, 2018, doi: https://doi.org/10.18769/ijasos.455663.
L. Tang and H. Liu, “Community Detection and Mining in Social Media,” Synthesis Lectures on Data Mining and Knowledge Discovery, vol. 2, no. 1, pp. 1–137, 2010, doi: https://doi.org/10.2200/s00298ed1v01y201009dmk003.
M. Atzmueller, “Mining social media: key players, sentiments, and communities,” Wiley Interdisciplinary Reviews: Data Mining and Knowledge Discovery, vol. 2, no. 5, pp. 411–419, 2012, doi: https://doi.org/10.1002/widm.1069.
E. M. Okoro, B. A. Abara, A. O. Umagba, A. A. Ajonye, and Z. S. Isa, “A hybrid approach to fake news detection on social media,” Nigerian Journal of Technology, vol. 37, no. 2, p. 454, 2018, doi: https://doi.org/10.4314/njt.v37i2.22.
K. E. Anderson, “Getting acquainted with social networks and apps: combating fake news on social media,” Library Hi Tech News, vol. 35, no. 3, pp. 1–6, 2018, doi: https://doi.org/10.1108/lhtn-02-2018-0010.
C. Edwards, “Ignorance is strength [fake news on social media],” Engineering & Technology, vol. 12, no. 4, pp. 36–39, May 2017, doi: https://doi.org/10.1049/et.2017.0402.
P. Singhal, P. Singh and A. Vidyarthi, “Interpretation and localization of Thorax diseases using DCNN in Chest X-Ray” Journal of Informatics Electrical and Elecrtonics Engineering, vol. 1 no. 1, pp. 1-7, 2020.
P. Singhal, P. Sharma, and B. Hazela, “End-to-end message authentication using CoAP over IoT,” in International Conference on Innovative Computing and Communications, Singapore: Springer Singapore, 2019, pp. 279–288.
P. Singhal, P. Sharma, and S. Rizvi, “Thwarting Sybil Attack by CAM Method in WSN using Cooja Simulator Framework,” International Journal of Engineering & Technology, vol. 8, no. 1.5, pp. 116–125, 2019.
P. Singhal, P. Sharma, and D. Arora, “An approach towards preventing iot based sybil attack based on contiki framework through cooja simulator,” Int. J. Eng. Technol., vol. 7, no. 2.8, p. 261-267, 2018.
S. Kumar, M.A. Wajeed, R. Kunabeva, et al., “Novel method for safeguarding personal health record in cloud connection using deep learning models,” Comput. Intell. Neurosci., vol. 2022, p. 3564436, 2022.
P. Singhal, P. K. Srivastava, A. K. Tiwari, and R. K. Shukla, “A survey: Approaches to facial detection and recognition with machine learning techniques,” in Proceedings of Second Doctoral Symposium on Computational Intelligence, Singapore: Springer Singapore, pp. 103–125, 2022,.
S. Kumar, P.K. Srivastava, A.K. Pal et al., “Protecting location privacy in cloud services,” J. Discrete Math. Sci. Cryptogr., vol. 25, no. 4, pp. 1053–1062, 2022.
S. Kumar, P. K. Srivastava, G. K. Srivastava, P. Singhal, D. Singh, and D. Goyal, “Chaos based image encryption security in cloud computing,” J. Discrete Math. Sci. Cryptogr., vol. 25, no. 4, pp. 1041–1051, 2022.
P. Srivastava, P. Singhal, S. Srivastava, and D. Kanojia, “Case Study: An Efficient Survey on Security Analysis of Social Networking,” ECS Transactions, vol. 107, no. 1, 2022.
A. K. Pandey, S. Kanchan, and A. K. Verma, “Applications of Fibonacci Sequences and Golden Ratio,” Journal of Informatics Electrical and Electronics Engineering, vol. 4, no. 1, pp. 1–11, 2023..
S. Islam and Department of Electrical & Electronics Engineering, AIUB, Bangladesh, “Improvement of Li-ion battery active balancer using PI-controller,” J. Infor. Electr. Electron. Eng., vol. 3, no. 2, pp. 1–10, 2022.
A. Srivastava and Department of Computer Science and Engineering, Amity School of Engineering and Technology Lucknow, Amity University Uttar Pradesh, India, “Handwritten digit image recognition using machine learning,” J. Infor. Electr. Electron. Eng., vol. 3, no. 2, pp. 1–11, 2022.
Downloads
Published
How to Cite
CITATION COUNT
Issue
Section
License
Copyright (c) 2023 Yuvraj Singh, Dr. Pawan Singh

This work is licensed under a Creative Commons Attribution 4.0 International License.